Request KYC documents using the Rebilly API
This topic describes how to request Know Your Customer (KYC) documents from customers using the Rebilly API. The KYC process compares customer data against data in documents to verify a match. For information on KYC and how to use it in the Rebilly UI, see KYC.
To use this features, you must activate the Rebilly KYC add-on. For more information, see KYC & AML.
Prerequisites
To complete this guide, you need customer data. To obtain customer data, see Retrieve a customer or Upsert a customer.
Gathering docs
Create a PostKycRequest.
The following is a sample request body.
{ "documents": [ { "type": "identity-proof", "faceProofRequired": true } ], "redirectUrl": "http://example.com", "customerId": "abc123" }The following is a sample response body.
{ "id": "4f6cf35x-2c4y-483z-a0a9-158621f77a21", "documents": [ { "type": "identity-proof", "maxAttempts": 3, "faceProofRequired": true } ], "status": "pending", "redirectUrl": "http://example.com", "expirationTime": "2022-08-24T14:15:22Z", "createdTime": "2022-08-24T14:15:22Z", "updatedTime": "2022-08-24T14:15:22Z", "customerId": "abc123", "reason": "", "matchLevel": 2, "_links": [ { "rel": "self", "href": "https://example.rebilly.com" }, { "rel": "kycGatherer", "href": "https://verification.comply.services/?token=123" } ] }If the response
statusisfulfilledthe process is complete, which might happen with an instant process such as a credit file lookup. The response includes a related linkkycGathererresource in the_linkscollection. Use the correspondinghrefvalue in the next step.Redirect the customer to the
hrefvalue of thatkycGathererlink. When the customer completes the process, they return to theredirectUrlwith aninfoquery parameter appended to the URL.
Webhooks
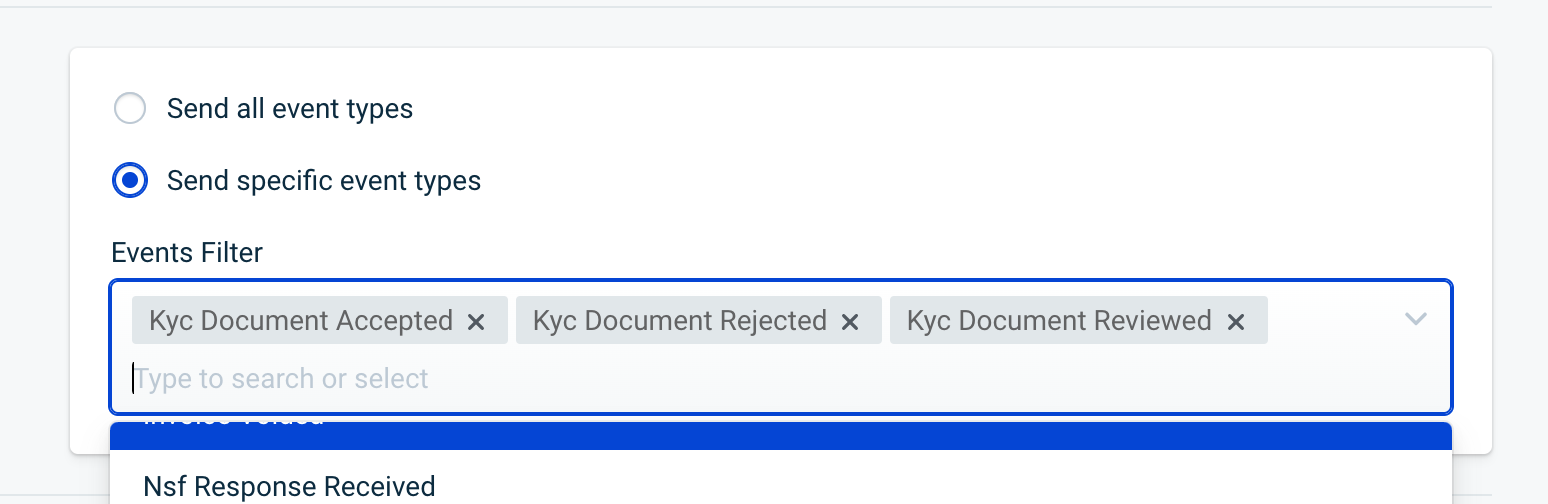
Use webhooks to stay updated about the status of KYC documents. Subscribe to these events:
- KYC request fulfilled
- KYC document modified
- KYC document reviewed
- KYC document accepted
- KYC document rejected